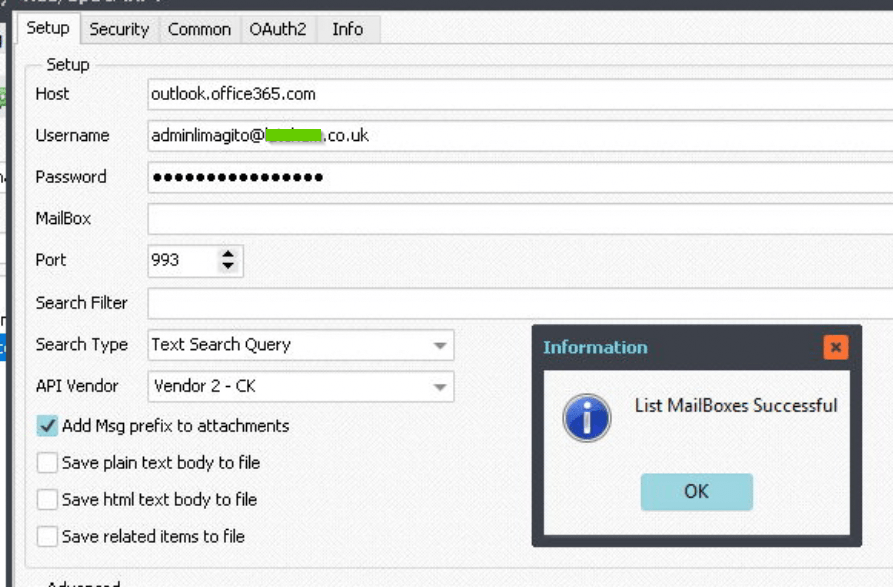
Q: I am now trying to connect to a shared mailbox in 365, can you please assist on how I can do this? The authentication is working fine against the user mailbox [A] but I’m not sure how to modify the IMAP4 setup to connect to a shared mailbox.
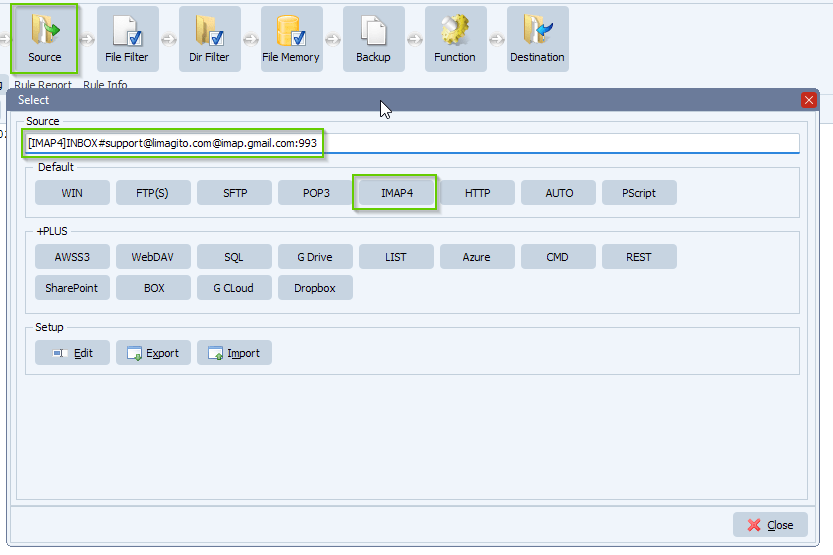
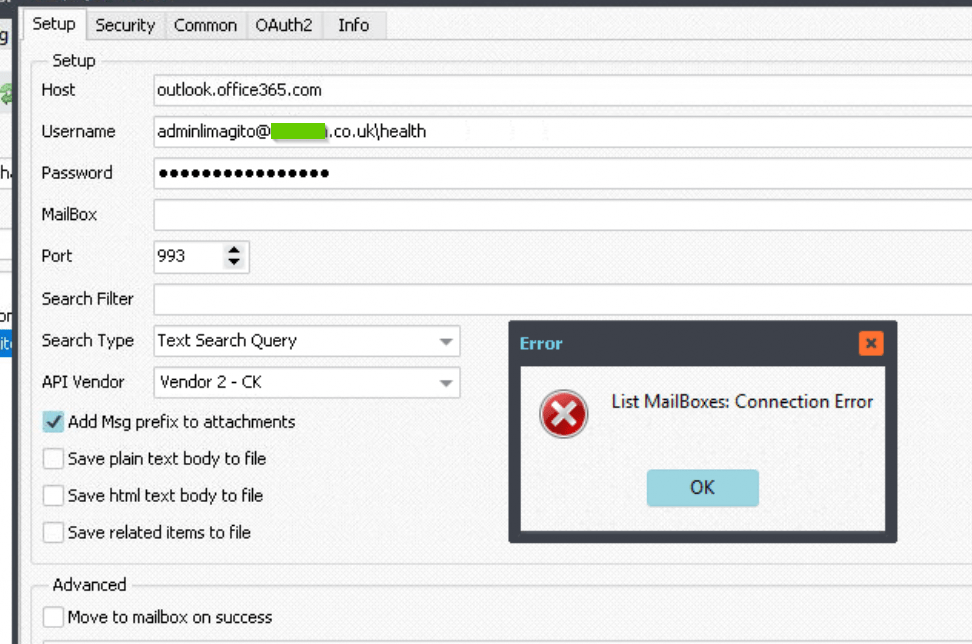
Source: [IMAP4]#adminlimagito@mycompany.co.uk@outlook.office365.com:993
MailUser: adminlimagito@mycompany.co.uk
Shared mail: health@mycompany.co.uk – mailbox permissions setup, email apps enabled
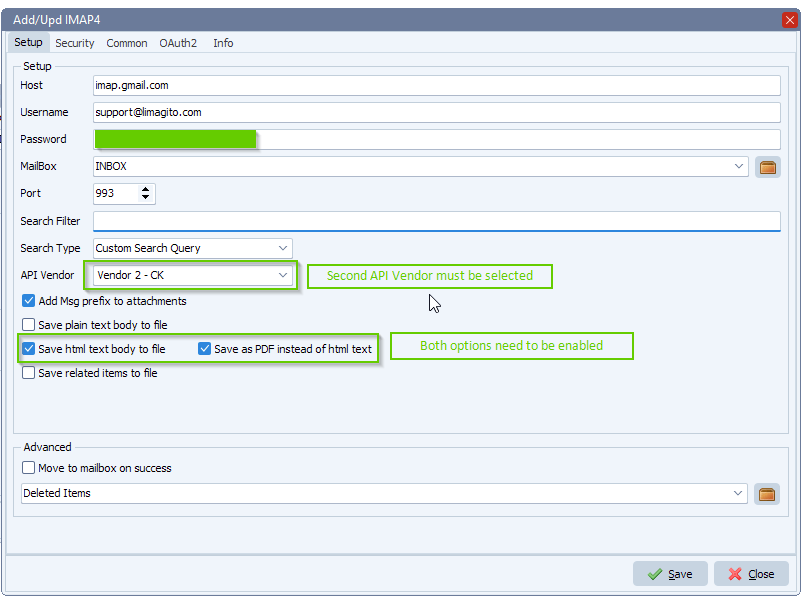
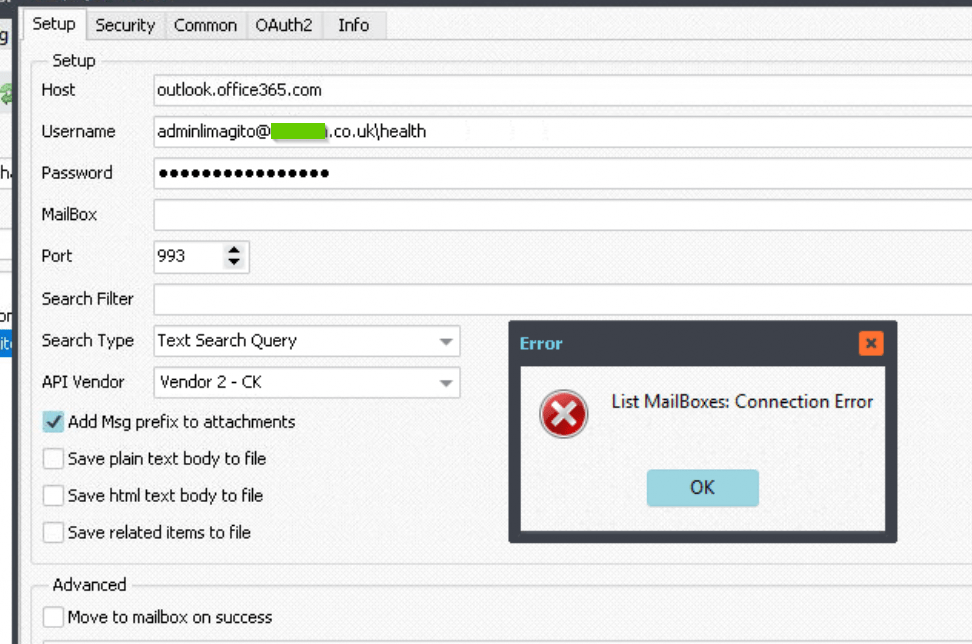
I’ve tried using: adminlimagito@mycompany.co.uk\health in the username and various other option all without success [B]
If I put health@mycompany.co.uk in the Mailbox I think it ignores this and connects to the user mailbox.
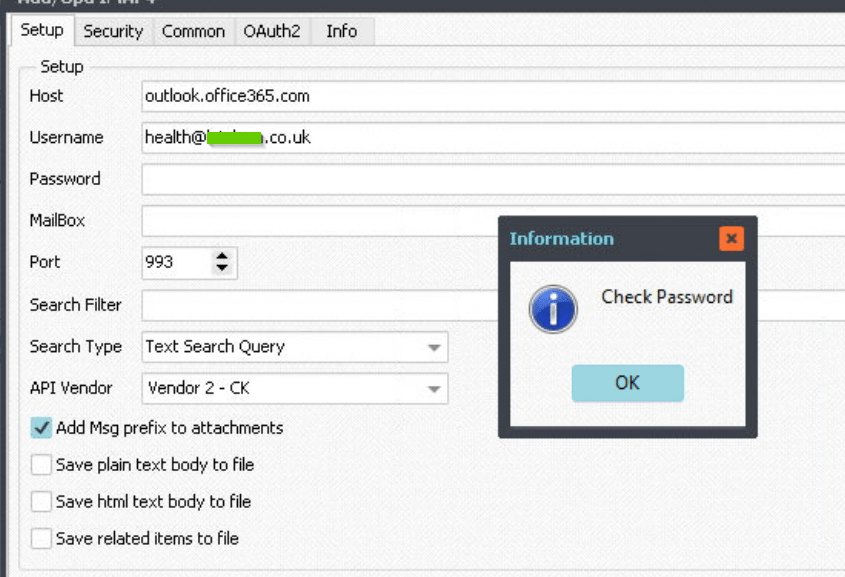
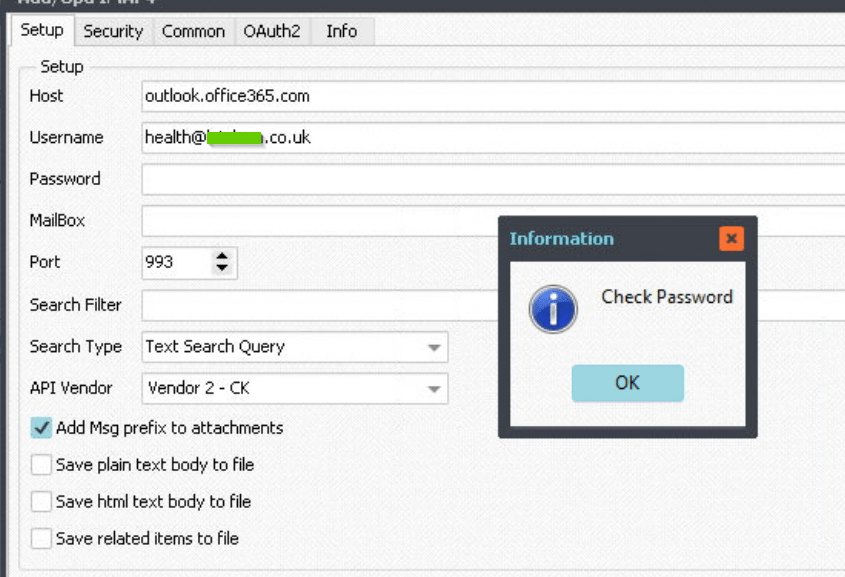
If I follow the instructions https://limagito.com/is-there-a-possibility-to-access-a-shared-office-365-mailbox-with-imap/ it returns error ‘Check Password’ [C]
Many thanks, Adam
[A]
[B]
[C]
– Limagito:
Hello Adam,
According to our information (confirmed by a user) you should enter the shared mail address as username (health@mycompany.co.uk)
The reason why in our article the password is left blank is because our user was using OAuth2 authentication.
( https://limagito.com/connecting-to-office-365-email-using-imap-and-oauth2-authentication/ )
That is why you get the ‘Check Password’ Messagebox.
Question, what happens when you enter health@mycompany.co.uk as username and the password from the admin account (adminlimagito@mycompany.co.uk).
– Customer:
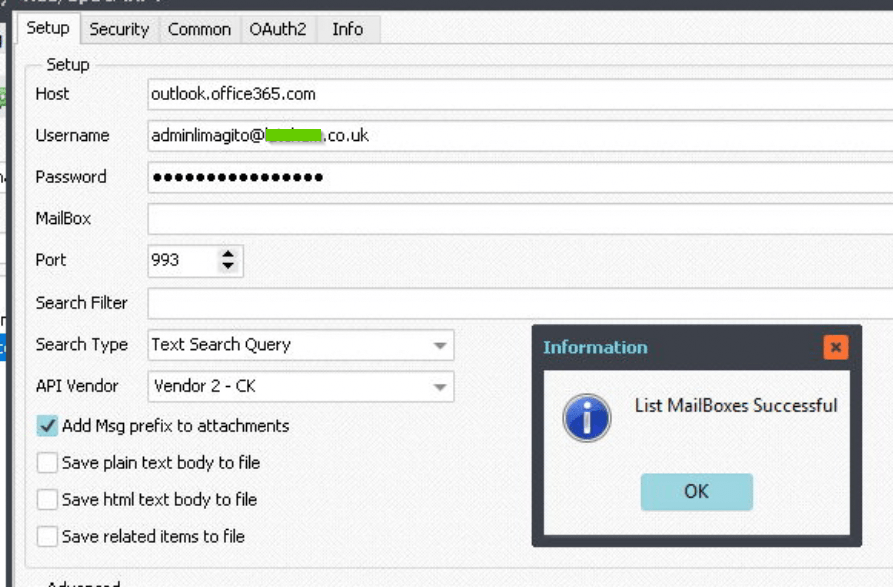
As suggested I changed the username to health@mycompany.co.uk
And left the password is it was for the admin account (adminlimagito@mycompany.co.uk).
This now lists the health mailbox!
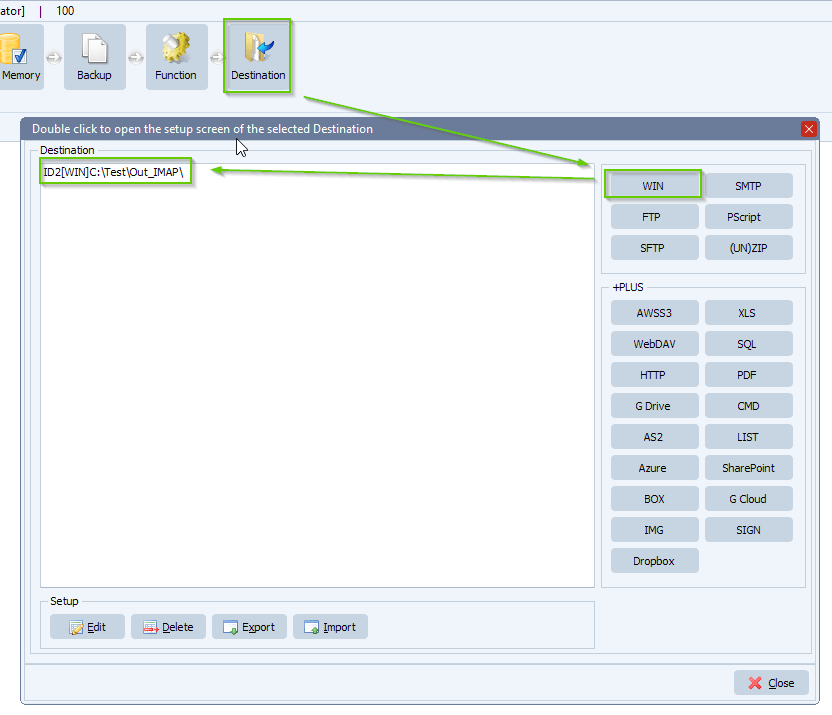
The source is now: [IMAP4]health#health@mycompany.co.uk@outlook.office365.com:993
I would not have thought to try exactly that. One for your (&mine) documentation perhaps
Thanks again for your quick response 😊
Adam
#FileTransfer #imap
If you need any
info about this post, please let us know.
Best regards,
Limagito Team